The data and security sections are two of the most fundamentally important sections of the CTA. They are closely interconnected and span across the entire CTA scenario. A CTA candidate must pass all the seven sections in the board exam. However, doing well in these two sections is imperative and this session will explore the reasons as to why this is the case.
Two fundamental sections in the CTA
All the seven sections in the CTA exam are equally important. But your chances of doing well can be boosted by getting these two sections right.
- Data
- Security
Recognise that all the requirements in the scenario need to come together in your solution in a coherent fashion. Understanding the data elements in the scenario and their lifecycle is critical. Demonstrating that you can secure not just the data but the whole solution in general is important. This session serves to emphasise on the importance of these two fundamental sections.
Data – Exam Outline
Given a scenario, describe the platform architecture considerations, platform impact and optimization methods used when working with large data volumes. Given a scenario, describe data modeling concepts and implications of database design and modeling. Given a scenario, determine the data migration strategy, considerations, and appropriate tools to use.
From: https://trailhead.salesforce.com/en/help?article=Salesforce-Certified-Technical-Architect-Exam-Guide
Why is the Data Model so important?
Arguably the most important artifact in the exam. Identifies all the key data entities (objects) in the scenario. Has a direct impact on
- License choices
- Sharing and Visibility
- Data Migration and archival
- Solution Architecture
- Integration
- Reporting
- Org strategy
Should convey the following to the judges
- Objects and relationships (LU/MD/Self/external).
- Ownership
- Cardinality
- LDV
- Sharing (OWD for int and ext)
- Relevant data residing externally
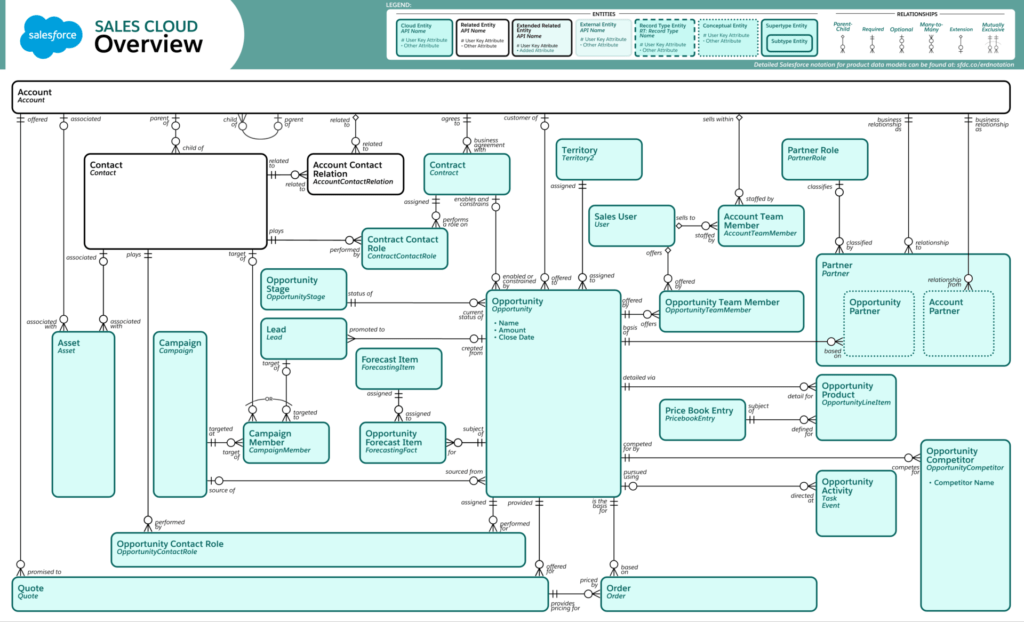
From https://architect.salesforce.com/design/architecture-gallery/sales-cloud-overview-data-model
How I studied for the data section?
Went back to basics and learn about Relational database concepts.
- ER Modelling
- Normalised forms / Denormalisation
- Understand how SF differs from relational databases
- Looked up general industry data models and reviewed them – Hotel reservation, Event management, Vehicle dealerships etc
- Data models for – Uber, AirBNB, SpaceX etc
- Behaviour of junction objects
- Acknowledged and fixed my blind spots!
Review and practice SF standard data models. Reviewed the SF industry cloud data models. Fiddle with Schema Builder in your developer org. Practice! Practice! Practice! to Develop muscle memory for speed.
Data Model Patterns
Understand other clouds like CPQ and FSL etc.
- No need to learn in depth
- Understand when they can help extend core SF to solve a requirement
- Maybe overkill to suggest without good justification.
Look at industry cloud data models and identify patterns to use.
- FSL data model: https://developer.salesforce.com/docs/atlas.en-us.field_service_dev.meta/field_service_dev/fsl_dev_soap_core.htm
- CPQ Data model: https://force365.files.wordpress.com/2018/03/salesforce-cpq-object-model.pdf (Don’t ask why)
- NPSP cloud data model: https://s3-us-west-2.amazonaws.com/sfdo-docs/npsp_entity_relationship_diagram.pdf
- Education Cloud data model: https://www.salesforce.org/wp-content/uploads/2018/08/HEDA-student-record.jpg
- FSC data model: https://developer.salesforce.com/docs/atlas.en-us.financial_services_cloud_admin_guide.meta/financial_services_cloud_admin_guide/fsc_admin_data_model_diagram.htm
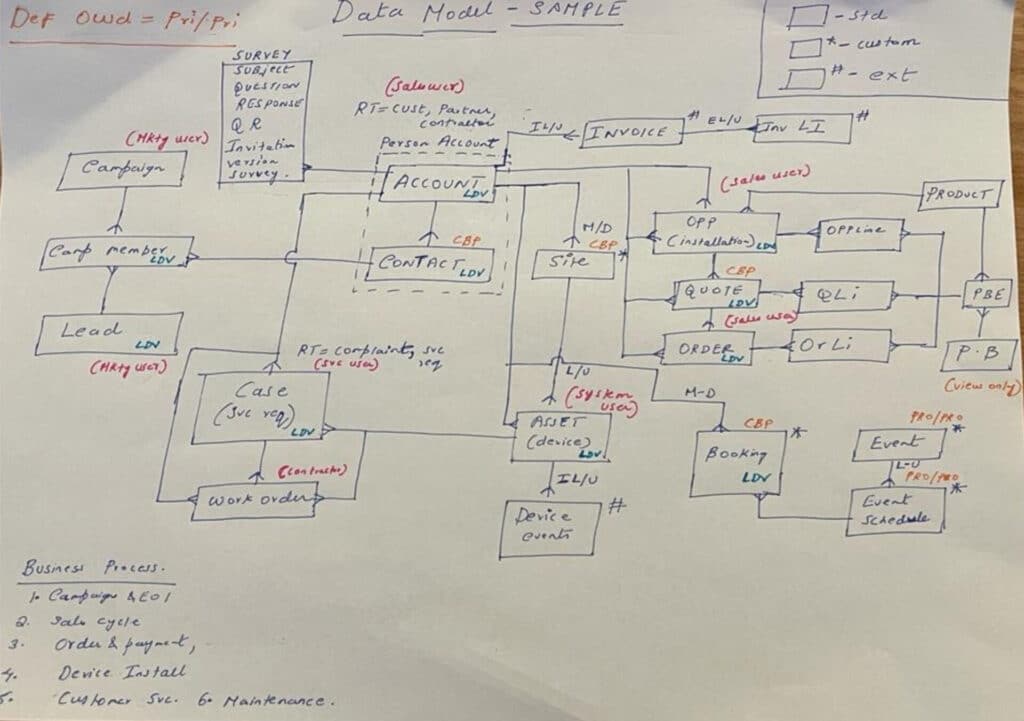
Data Model : Tips
Identify the objects as you are solving the scenario. Maybe best to create a rough working copy. Goal: Optimal data model which solves the requirements with relevant justification. Key decisions
- Standard v/s custom
- External object and their relationships
- Do licenses cater for it?
- Satisfies solution requirements?
- Satisfies sharing requirements
Save time by having ready made patterns for objects
- Lead, Opp, Order for sales.
- Probably need Account, Contact (And/ Or Person Account), Case at a minimum
- Record types for the key objects
- External objects with their considerations
Additional clues in sharing and reporting sections.
- Missing objects
- Field with FLS v/s custom object
- Denormalized objects for better reporting?
Try not to miss any objects. If there are very few objects in your DM, chances are that you are missing some.
- Solve for the scope of the requirements. Don’t over analyse.
When presenting, you have to weave a compelling story with your data model that explains end-to-end business requirements.
Remember you can change the DM in Q&A. Don’t be afraid to do so.
Data Model – Sample
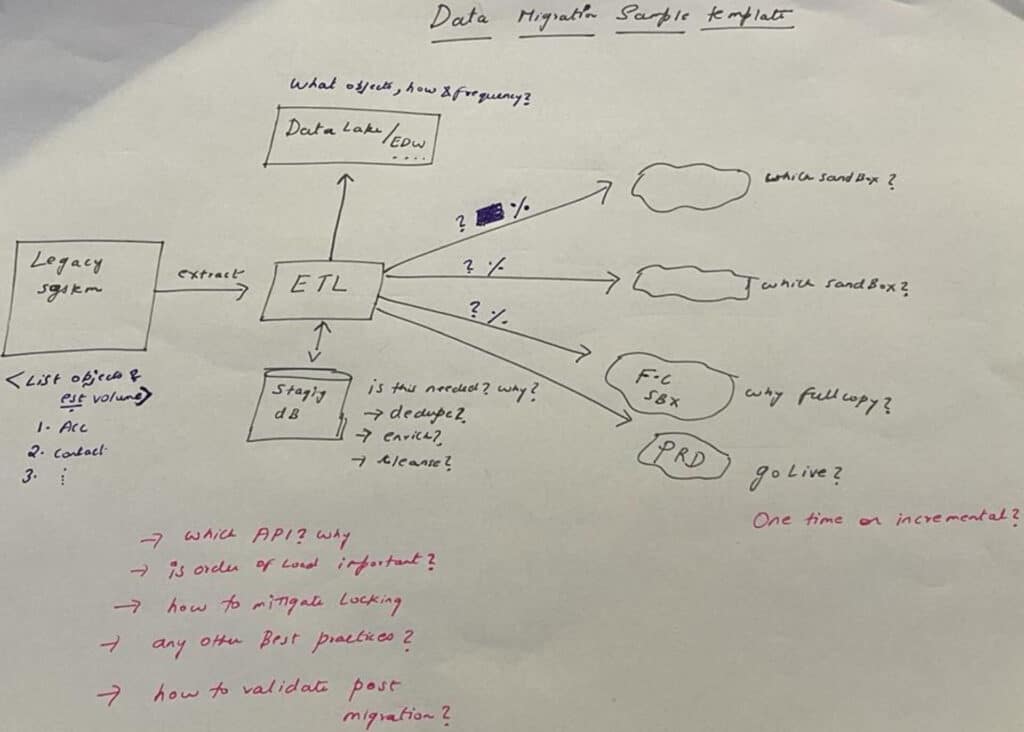
Data Migration – Tips
Please check this post to learn about Data Migration Tips and trick here. Here is some data migration tips.
- First stage of life cycle of your data. How is it entering SF and what is it used for?
- Have a template and describe the overarching plan. Include:
- Key objects and estimated volume.
- Don’t forget files and Knowledge Articles
- How data is prepared prior to load?
- Testing the data load in sandboxes
- Go-live plan – Big bang v/s Staggered incremental approach (Don’t forget the why?)
- Best practices
- Do not forget the archival process.
- Where is the data archived to? – With justifications
- EDW
- Big Objects
- Heroku
- AppExchange backup/recovery
- How is the archival process done and what is the frequency?
- How much data should reside on platform – Review reporting requirements
- How is external data accessed in SF when required?
- Where is the data archived to? – With justifications
- Do not forget individual requirements. Tie back the solution to the requirement.
- Options to verify that the data migration was successful?
- Governance, reporting and other project requirements may have an impact.
Data Migration – Sample
Large Data Volumes (LDV) in Salesforce
A “large data volume” is an imprecise, elastic term. These large data volumes (LDV) can lead to sluggish performance, including slower queries, slower search and list views, and slower sandbox refreshing. Probably the easiest section in Data.
- Identify the LDV objects. Pay attention to the junction objects.
- Estimate the volume based on future growth
- Do the math
- Leverage Google sheets to do the calculations
- Have templates ready – YoY growth over X years
- Provide mitigations with relevant justifications. Be prescriptive.
- Indexes – Be specific. Standard v/s custom fields.
- Make queries selective / filters
- Archival – Be specific.
- Skinny tables etc
- Read up and learn the following:
- Query optimisation and review this
- Query plan tool
- Read the LDV whitepaper and review again.
- Ownership and lookup skews
- Another whitepaper to review
- Parallel sharing rule recalculation
- Deferred sharing maintenance
- Granular locking
Security
Security – Exam Outline
Given a set of requirements, architect a solution that utilizes the appropriate platform security mechanisms. Given a scenario, identify the security considerations and risks, and leverage the appropriate security capabilities to design a secure portal architecture including access by both internal and external users.
Given a scenario, identify the declarative platform security features that can be used to meet record-level security requirements. Given a scenario, identify the programmatic platform security features that can be used to meet security requirements.
Given a scenario, describe how to incorporate the platform security features into a solution to give users the appropriate object and field access permissions. Given a set of requirements, design and justify an end-to-end identity management solution.
From: https://trailhead.salesforce.com/en/help?article=Salesforce-Certified-Technical-Architect-Exam-Guide
Security – Where to Start?
A formidable opponent in the CTA.
- Like the Data section, it also encompasses almost all areas of your solution.
- Secure your data in the org
- Object level security – CRUD / FLS
- Record level security using the the most optimal options.
- Secure data in transit
- Security for integrations
- 2 way SSL for inbound v/s outbound using certificates
- Payment gateways and PII compliance
- Security for integrations
- Secure data at rest
- Options to encrypt data and files
- Classic v/s Platform Encryption
- How does Shield PE work? What else can it protect?
- IDAM
- Super important. No need to say anything here.
- Monitoring
- Event Monitoring
- Enhanced Transaction Policies
Secure data in SF
- Keep tracking the sharing reqs for key objects and denote the OWD in the data model.
- Who owns it and who will it be shared with and how?
- Be well versed in all the declarative SF sharing features
- OWD
- Role Hierarchy is important
- OBSR, CBSR, Public Groups, Territories and their limits. They should match the RH.
- Everything should work together and scale!
- Experience Site (Community) access is critical
- Sharing Sets and groups
- Customer Community license
- Case ownership, access and routing
- Delegated ext admin and Super user
- Know all the features in and out.
- Implicit sharing, M-D relationship
- Manual sharing and Teams
- Account Data relationship rules
- Keep it simple but do not ignore Programmatic sharing
- Practice how you will solve and present precisely and succinctly
- Do not duplicate answers (Example: SSO slide will cover IDAM)
Security – Some things to ponder
- How are customer accounts created and who owns them?
- How do partners get access to customer data?
- How is an Opportunity record shared between two or more partners?
- How do you give and take away temporary access to a record?
- How is the OWD of some standard objects controlled?
- Example: Contact, Quote etc
- New features and updates (which are GA) such as:
- Restriction Rules
- OWD for Product (Enforced Summer’ 22)
- Threat Detection
IDAM – Key things to know
- Authentication and single sign-on
- Propose a SSO solution with an IdP and justify – MS Azure AD v/s ADFS v/s Ping /Okta and when to use each?
- SF as IdP, SF as SP , SF as both? , myDomain
- Types: Federated with SAML and Delegated
- Review all the SSO flows. Make sure to explain the context of your scenario.
- Hands-on practice with Azure AD / Ping, Okta etc. How to set up?
- Provisioning and de-prov
- Canvas and its authentication flows
- Social Sign On
- OpenID Connect
- How to set up
- Auth Provider
- Reg Handler (know key use cases)
- Config in the exp site
- Authorisation
- How does Salesforce support OAuth 2.0? Basics here in my DF video from 2017.
- Connected App and all the options and scope?
- Review the OAuth flows and know them well. Key entities that are exchanged?
- What are the different tokens and which flows support them?
- Connected Apps have a section to enable SAML. What use case does it solve?
- SSO + OAuth
- Understand how nested flows work
- Practice drawing and explaining them well.
- I practiced every flow from this. Thank you Lawrence Newcombe.
Misc security topics
- In additional to everything covered in the Sharing and Visibility cert, you need to review and know the Salesforce Security Guide
- Key additional topics that I focussed on include:
- MFA and the different ways to achieve this.
- SF session security and options
- Review Cryptography basics
- How do login flows work?
- How does SF health check and portal health check work?
- Vulnerabilities like XSS, CSRF, SOQL injection etc and how to mitigate
- SF Shield PE in-depth and what does it protect against?
- Real time event monitoring and what options exist for transaction security?
- Options to monitor SF security such as logins, set up audit trail etc
- Secure Apex, VF and LWC coding practices. (Ex: With Sharing v/s Without sharing, inherited sharing etc)
- Apex Crypto functions and when to use
- Protected Custom Settings and Custom Metadata types
- Understand how record sharing works in-depth.
- Create flashcards using any of your favorite methods (ANKI or anything other tool you prefer) to review important stuff.
- Practice and test as many security features as you can in your dev sandbox or TH playground!
Core study material
- Salesforce help articles – https://help.salesforce.com/s/?language=en_US
- Salesforce whitepapers – Sharing Architecture
- Salesforce Architect blog
- Salesforce Architect site
- The CTA mock scenarios
- CTA exam guide
- Youtube is a treasure chest
Recording
Summary
Data and security are two of the most important sections in the CTA. I suggest to prioritise your preparation strategies to ensure good coverage of important topics. Study extensively for the domain certs. Don’t do it only for the passing score. Solving these sections correctly and then presenting them confidently will go a long way in your CTA board. Keep it simple with good justifications. Assumptions are your friend. Thank you and all the best for your #JourneyToCTA!