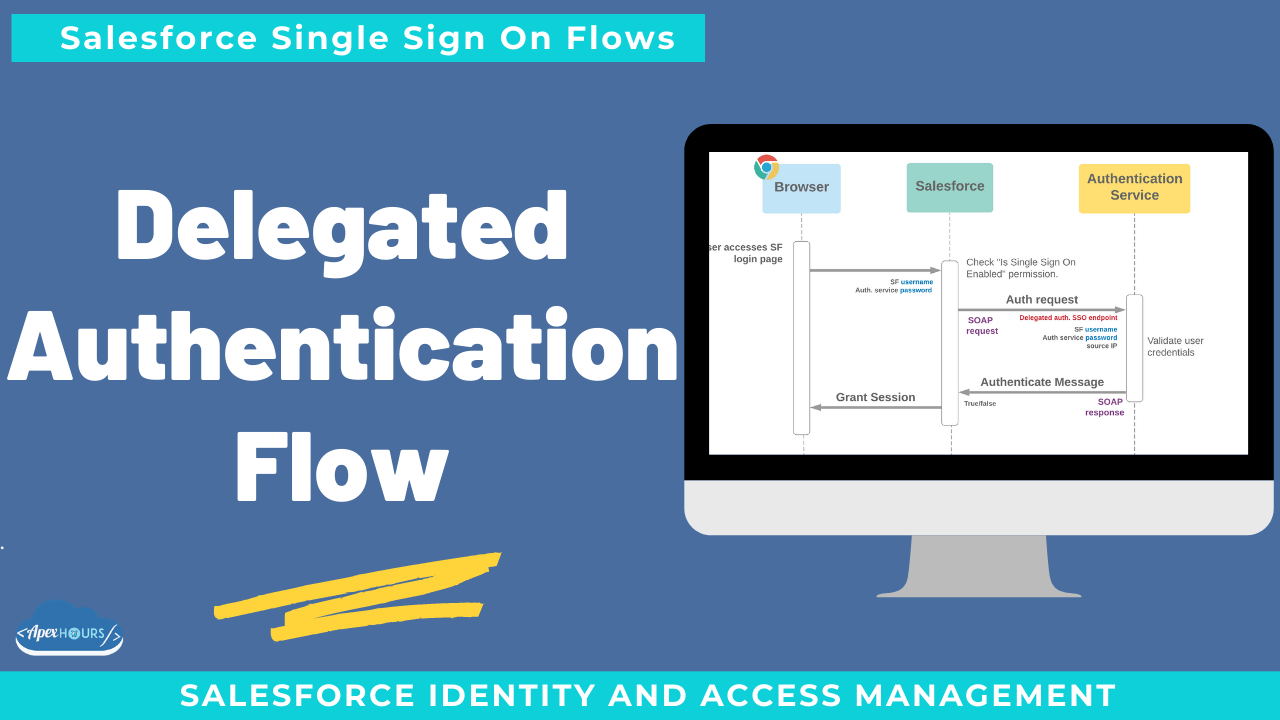
Delegated authentication flow in Salesforce allows us to accept a user’s credentials/authentication token, but pass it to an external service for validation. This is similar to single sign-on (SSO), but it offers a slightly different experience to users.
With this, one system relies on another system to validate user credentials. For example, you can configure your Salesforce org to rely on a Lightweight Directory Access Protocol (LDAP) server to validate credentials. Both SSO and delegated authentication enable users to log in to multiple apps with one set of credentials. However, with delegated authentication, users must log in to each app separately.
Basic requirements
- Authentication gateway provides SOAP web service which complies with Salesforce delegated authentication WSDL
- It is enabled in Salesforce and gateway endpoint URL added
What else to know
- Is Single Sign-On Enabled permission
- Directs users’ login credentials to the authentication service
- Password management functionality disabled
- Multi-factor authentication must use other Salesforce methods
Considerations for choosing Delegated Authentication
- Helpful to support SSO from legacy systems without SAML / OpenID Connect
- Using the basic flow (without authentication tokens), plain text passwords exposed to more systems
- Password reminders & resets may be less intuitive
- No native capability to share attributes from authentication gateway with Salesforce



Great session.I am just wondering if you have any use case of setting up JIT for new customer with Delegated authentication. Not sure if this is a valid scenario?