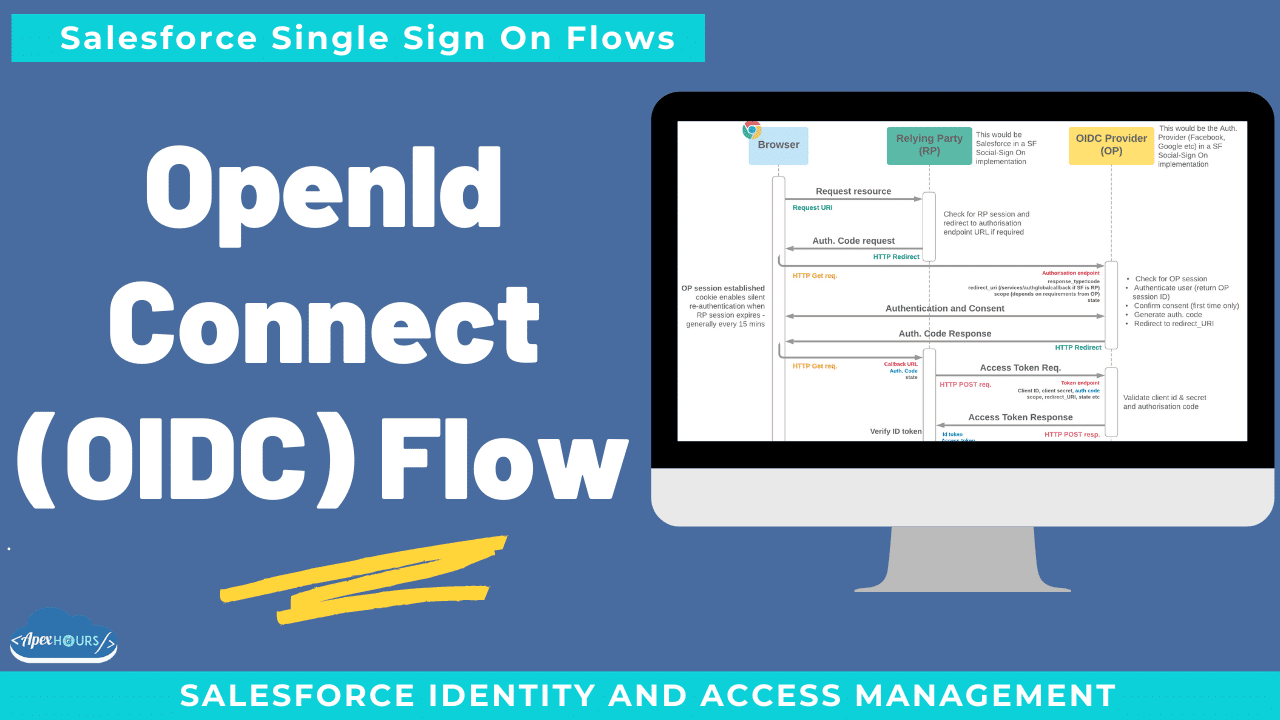
Allows confirmation of identity through an extended version of OAuth 2.0. OpenId Connect authenticate users without having to get your hands dirty with passwords. Consume OpenID Connect from popular Identity providers with Social Sign-On. Provide a single, branded Identity to your own users and applications using OpenID Connect.
Use any third-party web app that implements the server side of the OpenID Connect protocol as an authentication provider, such as Amazon, Google, and PayPal.
Basic requirements
- Participating systems are OAuth 2.0 enabled, and support secure HTTPS traffic
- Authorisation endpoint, client ID and secret must be configured in the Relying Party (RP) – the system the user wants access to
- OpenID Connect Provider (OP) must offer at least an authorisation endpoint, and usually token and UserInfo endpoints too
- OP is configured with redirect_uri endpoint(s), or offers dynamic endpoint registration
What else to know
- RESTful implementation with lightweight JWTs for user attributes
- Either web server or user-agent (browser only) flavours possible
- Existing User Linking
- Single Logout
- Custom OpenID Connect providers can be configured as Salesforce Authentication Providers
- Salesforce uses OpenID Connect or similar OAuth based protocols for its standard Auth. Provider options:
- Google & Microsoft offer OpenID Connect services
- Facebook has “Facebook Login”, based on OAuth2 and similar to OIDC
- Twitter provides “Log in with Twitter”, also based on OAuth2
- LinkedIn offers the “Member Authorization” API, also OAuth2
Recording
Considerations for choosing OpenID Connect
- With dynamic registration, OP does not need to “know” each RP, excellent choice for many external ID use cases
- User controls consent
- Lightweight REST/JWT protocols – much better for mobile
- Web server backchannel:
- Extra security layer
- Rich information transfer from UserInfo endpoint (pictures etc)
- Minor adaptation for a system supporting OAuth
- Less common than SAML in enterprise apps (but becoming more prevalent)



Hi,
Great video!
You mentioned that the redirect_uri can be configured in the Connected App upfront or dynamically.
I have a requirement that involves a dynamic endpoint but I can’t find any helpful documentation on this.
Can you help me out on this one?
Thanks!!