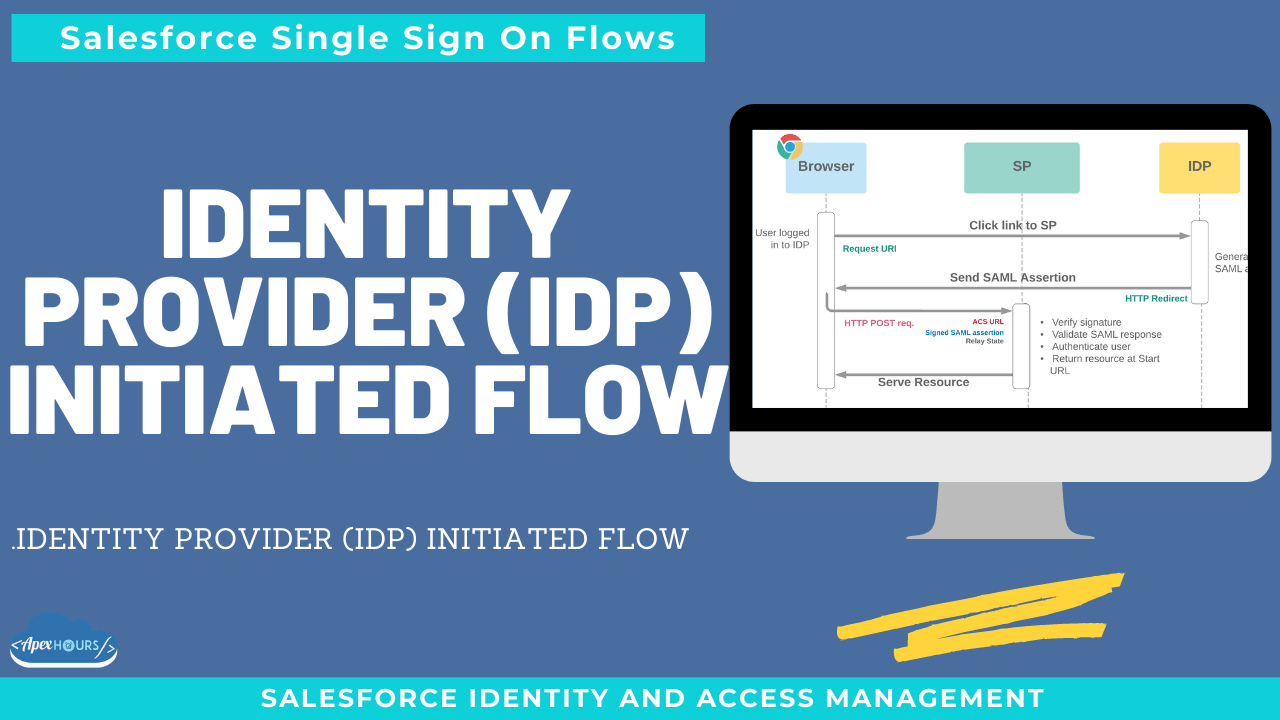
In this session we will talk Salesforce As Identity provider(IP). Allows an identity provider (IDP) to redirect to a service provider (SP) with a SAML assertion which confirms their identity and allows for automatic login.
NOTE: The system that authenticates users is called an identity provider. The system that trusts the identity provider for authentication is called the service provider
Basic requirements
- Participating systems support SAML 2.0 protocols and up to date recommended security countermeasures
- Certificate and entity ID from IDP configured in SP
- SAML ACS URL and entity ID from SP configured in IDP
- Does not require my domain
What else to know
- Most setup considerations similar to SP-initiated flow
- One key difference…
- No request (assertions are unsolicited)
- Therefore In ResponseTo attribute not set
- So SP cannot guarantee that assertion was supplied by the user who is authenticated
- Presents a risk of assertion theft or substitution where IDP is susceptible to CSRF
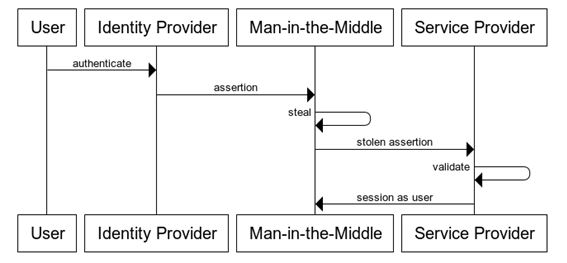
- Man-in-the-Middle attack
- Some mitigations can be made in the SP – no replays; accept only recent assertions; do not allow open redirects
Diagram source: https://www.identityserver.com/articles/the-dangers-of-saml-idp-initiated-sso
Considerations for choosing IDP-Initiated SSO
Don’t use unless you have to (and accept the security risk!)
- Legacy IDPs which don’t support SP-initiated SAML
- Scenarios where my domain is not practical
- Some canvas apps using SAML SSO
Other general considerations of SP-initiated SAML also apply
Recording
Identity Provider-Initiated SAML Flow
In an identity provider-initiated login flow, a SAML request is unnecessary because the identity provider starts the flow with a SAML response. An identity provider-initiated flow is a shortened version of a service provider-initiated flow. Here’s how this flow works:
- The user logs in to the identity provider.
- The user clicks a button or link to access the service provider.
- The identity provider initiates login by sending a cryptographically signed SAML response to the service provider. The SAML response contains a SAML assertion that tells the service provider who the user is.
- The service provider validates the signature in the SAML response and identifies the user.
- The user is now logged in to the service provider.