Join us to learn about Salesforce Shield Platform Encryption. Salesforce Shield is a trio of security tools that helps admins and developers build extra levels of trust, compliance, and governance right into business-critical apps. It includes Shield Platform Encryption, Event Monitoring, and Field Audit Trail. Ask your Salesforce administrator if Salesforce Shield is available in your organization.
What is Salesforce Shield Platform Encryption?
Shield Platform Encryption relies on a unique tenant secret that you control and a master secret that’s maintained by Salesforce. By default, we combine these secrets to create your unique data encryption key. You can also supply your own final data encryption key. We use your data encryption key to encrypt data that your users put into Salesforce and to decrypt data when your authorized users need it.
- Adds a new layer of security
- Encrypt sensitive data at rest
- Encryption key material is never saved or shared across orgs.
- Customer-driven encryption key
- Available for free in Developer Edition org.
Need for Shield Platform Encryption
We need Shield platform encryption for
- Compliance requirements
- Contractual obligations
Classic Encryption Vs Shield Platform Encryption
Let’s see what the difference is between Classic Encryption and Shield Platform Encryption.
| Feature | Classic Encryption | Platform Encryption |
| Pricing | Included in base user license | Additional fee applies |
| Encryption at Rest | Yes | Yes |
| Encryption Algorithm | 128-bit Advanced Encryption Standard (AES) | 256-bit Advanced Encryption Standard (AES) |
| Masking | Yes | No |
| Encrypted Standard Fields | No | Yes |
| Encrypted Custom Fields | Dedicated custom field type, limited to 175 characters | Yes |
| Manage Encryption Keys Permission | No | Yes |
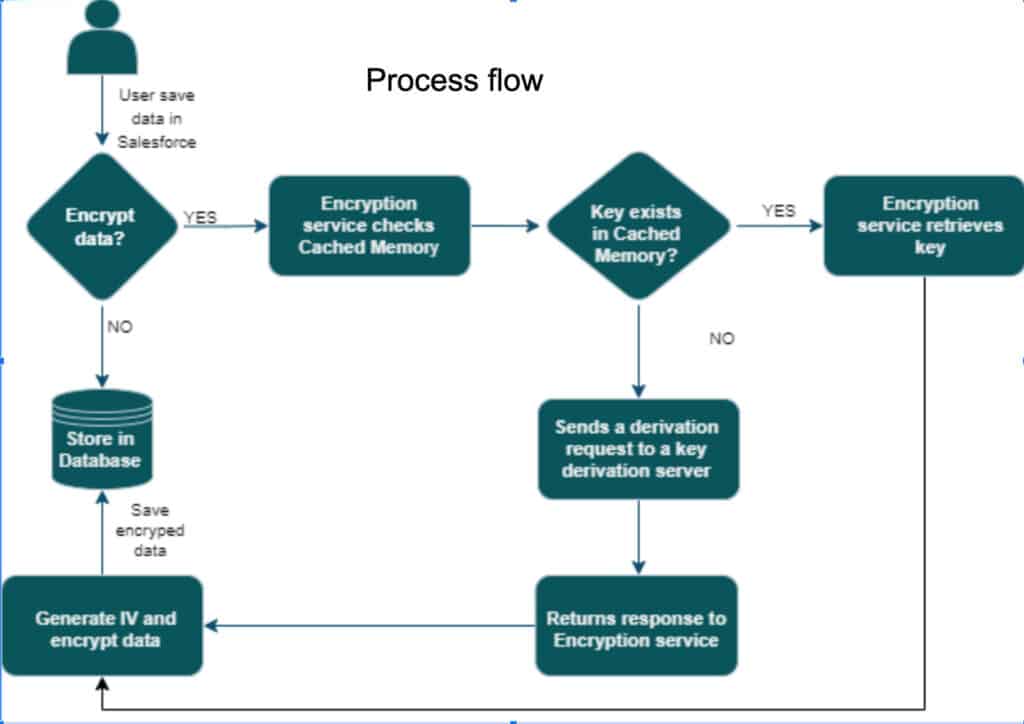
Shield Platform Encryption Process Flow
Let’s understand how the shield platform encryption works behind the screen.
Type of Salesforce Encryption
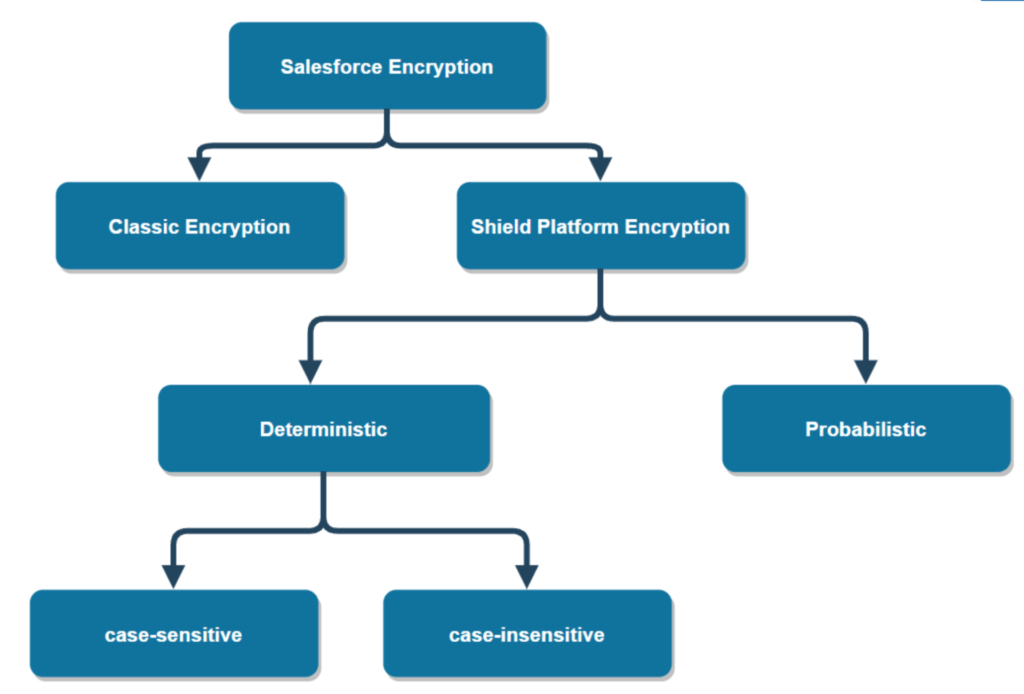
1. Probabilistic Encryption
- Introduces an element of chance.
- Source text repeatedly encrypted with the same key will normally yield different ciphertext.
- For example – ‘hello world’ won’t always correspond to the same ciphertext.
- By default, probabilistic encryption in Salesforce.
- No filtering.
- It is recommended to use probabilistic encryption whenever data in a field will not need to be filtered.
Custom Fields – Cannot
- encrypt custom fields in criteria-based sharing rules.
- Some custom fields can’t be encrypted.
- Schema Builder to create an encrypted custom field.
- Formula fields
SOQL/SOSL
Can’t include fields encrypted with the probabilistic encryption scheme in the following SOQL and SOSL clauses and functions:
- Aggregate functions such as MAX(), MIN(), and COUNT_DISTINCT()
- WHERE clause
- GROUP BY, ORDER BY clause
2. Deterministic Encryption
- Enable users to filter on encrypted data.
- Uses a static initialization vector (IV) so that encrypted data can be matched to a particular field value.
- Unique IV for a field in an org and can only be decrypted with your org-specific encryption key.
- Ciphertext- can be repeatedly produced, given the same source text and key.
- Example – ‘hello world’ == ‘&yy/ m/jyp’
- Case-Sensitive/Case-Insensitive
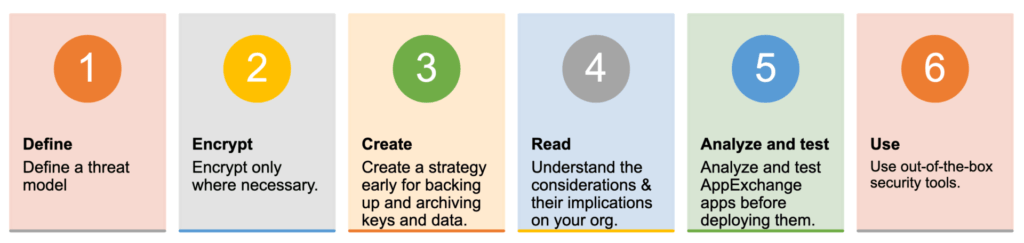
Planning for building apps with Platform Encryption
Salesforce Key Management and Rotation
Shield Platform Encryption lets you control and rotate the key material used to encrypt your data. You can use Salesforce to generate a tenant secret for you, which is then combined with a pre-release master secret to derive a data encryption key. You can also use the Bring Your Own Key (BYOK) service to upload your own key material or store key material outside of Salesforce and have the Cache-Only Key Service fetch your key material on demand.
1. Salesforce-generated encryption keys (Keys from Shield KMS)
Use the Shield Key Management Service (KMS) to generate your org-specific tenant secret for you. Shield Platform Encryption relies on a unique tenant secret that you control and a master secret that’s maintained by Salesforce. Salesforce combines these two secrets to create your unique data encryption key for data encryption and decryption.
2. Bring your own key (BYOK ) Tenant Secret
Use the infrastructure of your choice, such as an on-premises HSM, to generate and manage your tenant secret outside of Salesforce. Then, upload that tenant secret to the Salesforce KMS. This option is popularly known as “Bring Your Own Key,” although the element you’re really bringing is the tenant secret from which the key is derived.
Shield Platform Encryption relies on a unique BYOK tenant secret that you control and a master secret that’s maintained by Salesforce. Salesforce combines these two secrets to create your unique data encryption key for data encryption and decryption.
3. Opt-Out of Key Derivation with BYOK
Opt-out of the Shield KMS key derivation process with the Bring Your Own Key service. Use the infrastructure of your choice to create a data encryption key instead of a tenant secret. Then upload this data encryption key to the Shield KMS.
When you opt out of derivation on a key-by-key basis, the Shield KMS bypasses the derivation process and uses this key material as your final data encryption key. You can rotate customer-supplied data encryption keys just like you would rotate a customer-supplied tenant secret.
4. Cache-Only Key Service
Generate and store your key material outside of Salesforce using a key service of your choice, and use the Salesforce Cache-Only Key Service to fetch your key material on demand.
Your key service transmits your key material over a secure channel that you configure. It’s then encrypted and stored in the cache for immediate encrypt and decrypt operations.
Best Practices for Platform Encryption
Before implementing Salesforce shield platform encryption, let’s understand the best practices of platform encryption.
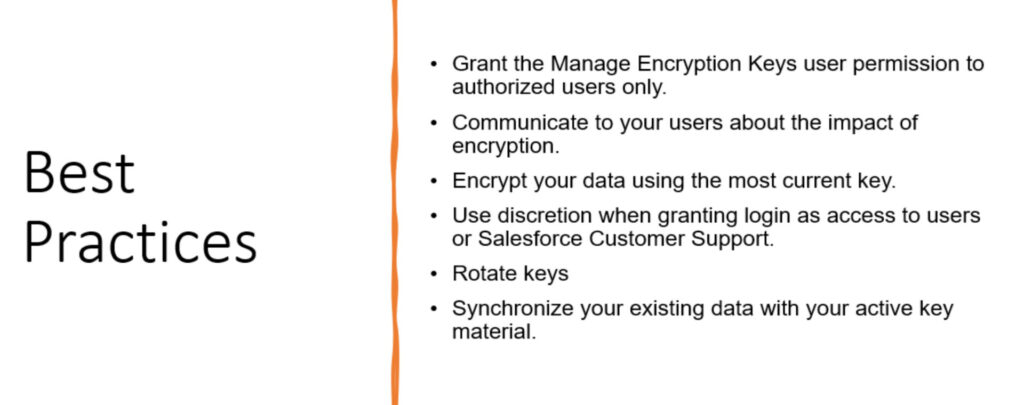
Key Management & Self-Service Background Encryption
Newly created and edited data are automatically encrypted with the most recent key. Existing data doesn’t automatically get encrypted. Self-Service Background Encryption. Synchronizing your data encryption doesn’t modify the record LastModifiedDate or LastModifiedById timestamps.
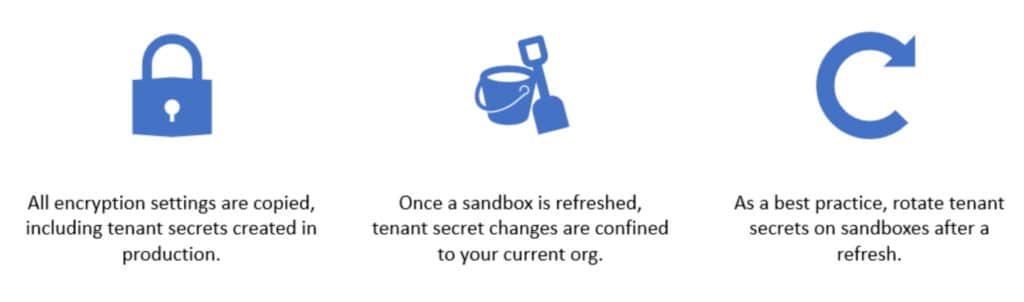
Shield Platform Encryption after sandbox refresh
Summary
Shield Platform Encryption allows you to natively encrypt your most sensitive data at rest across all your Salesforce apps. Encrypting data at rest adds another layer of protection to PII, sensitive, confidential, or proprietary data.



Thank you for sharing valuable information about Salesforce Shield. This article is beneficial who is looking for Salesforce Shield Services.
Can you provide me any case study regarding Salesforce Shield?
We will share Salesforce Shield case study soon