The ability to troubleshoot and audit your data is imperative to enforce governance across enterprise applications. This episode talks about the tools provided by Salesforce to troubleshoot implementations and audit changes to business data across the Salesforce org.
Audit & Troubleshoot Tool in Salesforce
1. Debug Logs
Debug logs are used to track the events information that occurs in your org.Debugs log will only be generated when you have an active flag turned on for the logged in user. A debug log can record database operations, system processes, and errors that occur when executing a transaction or running unit tests. Debug logs can contain information about:
- Database changes
- HTTP callouts
- Apex errors
- Resources used by Apex
- Automated workflow processes, such as:
- Workflow rules
- Assignment rules
- Approval processes
- Validation rules

2. Email Logs
- Email logs describe all emails sent through salesforce.com and can be used to help identify the status of an email delivery.
- Email logs are CSV files that provide information such as the email address of each email sender and its recipient, the date and time each email was sent, and any error code associated with each email.
- Logs are only available for the past 30 days.
3. Setup Audit Trails
- Setup audit trails gives you the picture of all the changes made in your org like Creating a User, Creating Trigger, Page, Component, Modifying any apex class or pages.
- The last 20 entries for your organization are listed below.
- You can download your organization’s setup audit trail for the last six months (Excel .csv file).
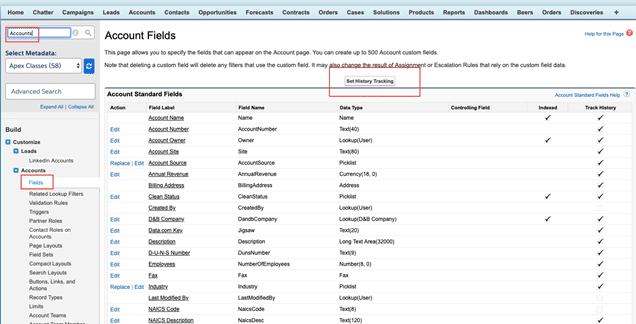
4. Field History Tracking
- Field history tracking is used to track the history of field values from old to new.
- To turn on the Field history for standard object go to Setup -> Customize -> Object Name -> Fields -> Click on “Set History Tracking”
5. Login History & IP White Listing
- Login History is used to track the Login information of the users
- IP Whitelisting is used to exclude the verification code by adding the IP ranges into Network Access
Audit & Troubleshoot Salesforce Data Demo
Further Learning
Here is playlist link for all recording
Monitoring & Auditing Tools in Salesforce
Learn more about Monitoring & Auditing Tools in Salesforce. There are different Monitoring & Auditing Tools are available in Salesforce. Here are some of them
- Salesforce Health Checker
- Portal Health Check
- Salesforce Optimizer
- Salesforce Accelerator
- Manual Org Assessment
- Security Center
- Login History
- View Setup Audit Trail
- System Overview
- Field History Tracking
- Lightning Usage App
- Apex Exception Emails
- Debug Logs
- Event Monitoring
- Transaction Security Policy
- API Usage Notification
- Force.com Code Scanner
- Apex PMD
- Custom Error Handling framework